Best Hardware Wallets for Crypto
If you are searching for the best cold wallet, start with a hardware wallet shortlist that balances security, backups, and everyday usability. This page ranks strong options for 2026.
Wallets Tested
Hours Research
Readers
Updated
Top picks
Updated for 2026 model releases, including the latest Trezor and Ledger devices.
- #1
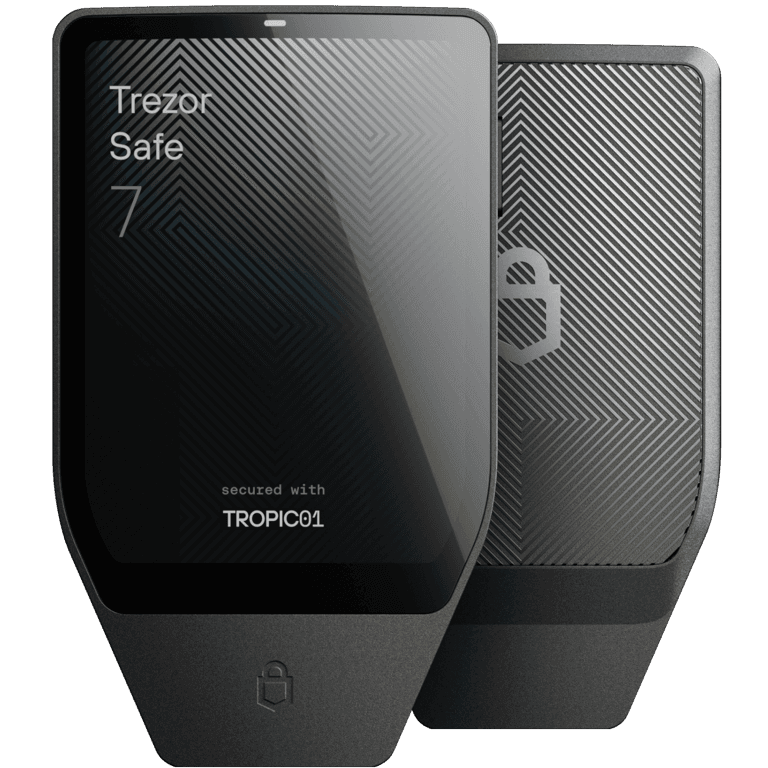
Trezor Safe 7
Latest Trezor flagship with modern hardware security and a premium on-device experience.
Most peopleUSB-C, Bluetooth, NFC$$$Security: Dual secure element with active post-quantum cryptography (SLH-DSA, ML-DSA)
Backup: Seed phrase with optional passphrase
- #2
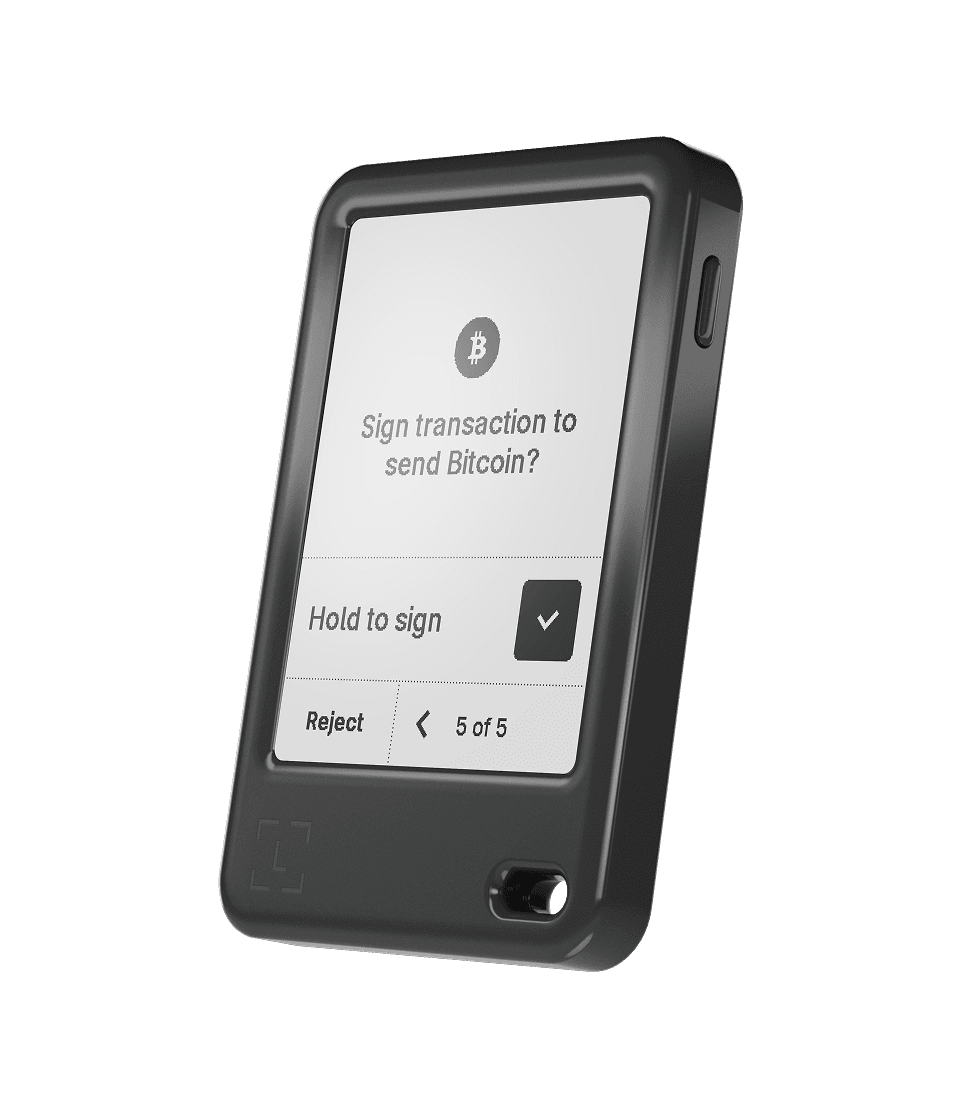
Ledger Nano Gen5
Latest Ledger Nano model for users who want touch navigation in a compact format.
Mobile-first usersUSB-C, Bluetooth, NFC$$Security: Secure element + Ledger OS with clear-signing workflow
Backup: Seed phrase with optional passphrase
- #3
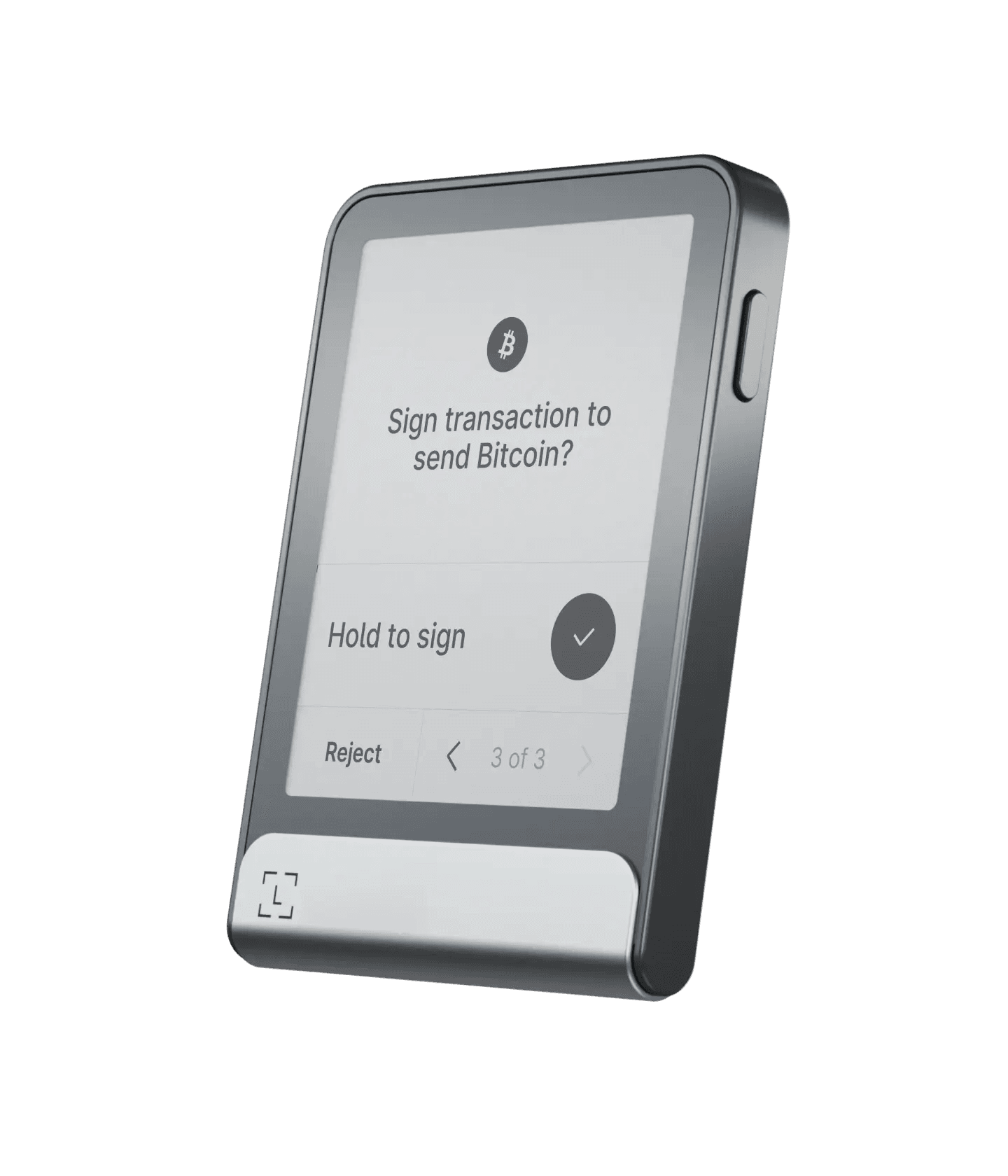
Ledger Flex
Modern Ledger touchscreen with easy review/sign flow and strong mobile usability.
Users who want a larger touchscreen signerUSB-C, Bluetooth, NFC$$$Security: Secure element + Ledger OS with clear-signing support
Backup: Seed phrase plus optional Ledger recovery options
- #4

Trezor Safe 5
Strong Trezor option if you want a premium touchscreen and mature backup flow.
Security-focused long-term holdersUSB-C$$Security: Open-source wallet stack with advanced on-device confirmations
Backup: Seed phrase with optional passphrase
- #5
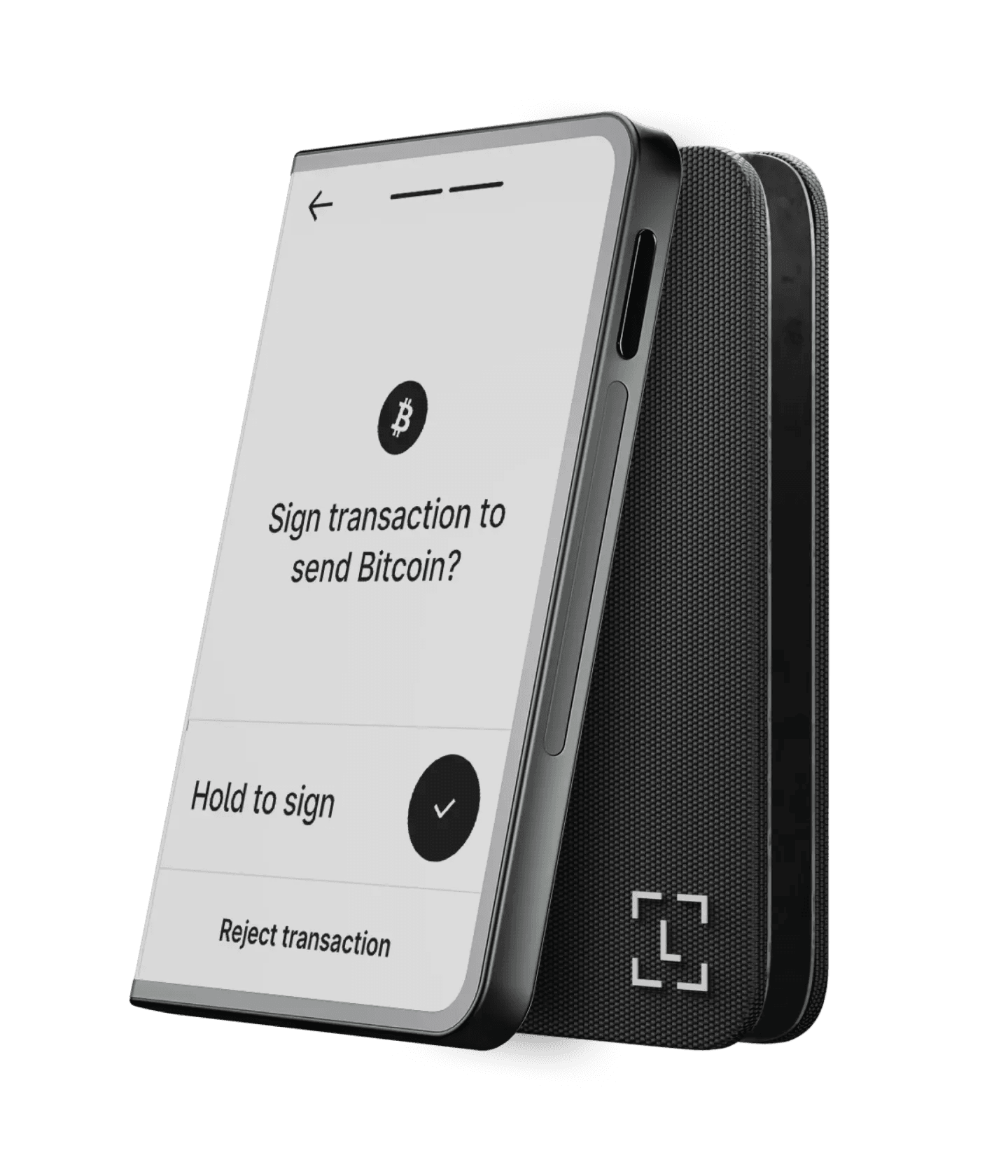
Ledger Stax
Flagship Ledger device with larger display for easier address and transaction review.
Premium touchscreen experienceUSB-C, Bluetooth, NFC$$$Security: Secure element + Ledger OS with clear-signing support
Backup: Seed phrase plus optional Ledger recovery options
Quick comparison
| Wallet | Best for | Connectivity | Price |
|---|---|---|---|
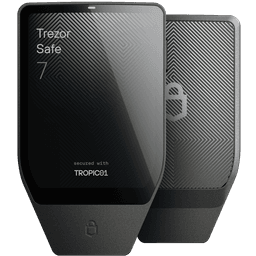 Trezor Safe 7 Trezor Safe 7 | Most people | USB-C, Bluetooth, NFC | $$$ |
 Ledger Nano Gen5 Ledger Nano Gen5 | Mobile-first users | USB-C, Bluetooth, NFC | $$ |
 Ledger Flex Ledger Flex | Users who want a larger touchscreen signer | USB-C, Bluetooth, NFC | $$$ |
 Trezor Safe 5 Trezor Safe 5 | Security-focused long-term holders | USB-C | $$ |
 Ledger Stax Ledger Stax | Premium touchscreen experience | USB-C, Bluetooth, NFC | $$$ |
Trezor vs Ledger
Trezor
- Fully open-source firmware
- Active post-quantum cryptography (Safe 7)
- Strong privacy (no mandatory account)
- Excellent recovery workflow
- Shamir Backup support for distributed recovery
- No mandatory app — works with third-party wallets
- Higher price point for latest models
- NFC limited to Safe 7 only
- Smaller ecosystem of native apps
Best for: Privacy-focused users who want full transparency and open-source assurance
Ledger
- NFC on most models
- Extensive coin/chain support
- Clear-signing workflow
- Multiple form factors (Nano, Flex, Stax)
- Largest hardware wallet ecosystem
- Bluetooth on most models for mobile use
- Not fully open-source
- Requires Ledger Live for setup
- Optional cloud recovery is controversial
- Past security incident (2020 customer data leak)
- Ledger Recover feature raised community concerns
Best for: Active traders who need broad coin support and mobile connectivity
Bottom Line
Choose Trezor if open-source transparency and privacy are your top priorities; choose Ledger if you need the widest asset support and mobile-friendly features.
Security features
Side-by-side comparison across all five wallets
Open Source
Secure Element
Passphrase Support
Clear Signing
PIN Protection
Anti-Tampering
Shamir Backup
Multi-Sig Support
Supply Chain Verification
Post-Quantum Ready
Air-gapped Option
Bluetooth
NFC
Coin Support
Hardware Wallet Setup Guide
Follow these steps to securely set up your hardware wallet.
- 1
Purchase from Official Source
~5 minBuy directly from manufacturer website. Never buy from third-party marketplaces.
Pro Tip
Check the manufacturer's website for authorized resellers in your country. Bookmark the official URL and double-check the domain before entering payment info to avoid phishing sites.
- 2
Verify Package Integrity
~2 minCheck tamper-evident seals. Compare serial numbers with manufacturer records.
Pro Tip
Take photos of the package and seals before opening. Some manufacturers provide online verification tools where you can enter the serial number to confirm authenticity.
- 3
Initialize Device Offline
~5 minSet up in a private space. Ensure no cameras or screens can capture your seed phrase.
Pro Tip
Use a Faraday bag or airplane mode on nearby devices for maximum security. Close all blinds and cover any smart devices with cameras in the room.
This step is critical for security. Any digital exposure of your seed phrase during setup could compromise your wallet permanently.
- 4
Write Down Recovery Phrase
~5 minWrite seed words on paper or metal backup. Never store digitally or photograph.
Pro Tip
Consider stamping your seed phrase on a metal plate for fire/flood resistance. Store copies in separate, secure physical locations such as a safe deposit box.
Your recovery phrase is the master key to your funds. If lost or exposed, your assets can never be recovered or could be stolen.
- 5
Verify Recovery Works
~8 minReset device and restore from seed phrase. Confirm access before storing real funds.
Pro Tip
Create a small test wallet first, restore it, then create your real wallet. This builds confidence in the recovery process and ensures your written phrase is correct.
- 6
Transfer a Small Test Amount
~5 minSend a small amount first. Verify you can send and receive before transferring large holdings.
Pro Tip
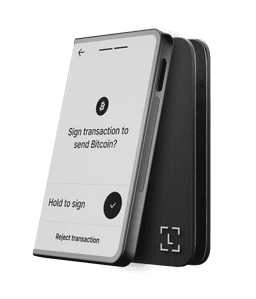
Wait for full confirmation of the test transaction before sending larger amounts. Compare the address on your hardware wallet screen with the one shown in your software — never trust the computer screen alone.
You're ready!
Your hardware wallet is set up and verified. You can now securely store and manage your crypto assets with confidence.
Security Best Practices
Essential tips to keep your crypto safe
Security Score
Follow all 9 tips to maximize your security
Critical
These are non-negotiable. Skipping any of these puts your funds at serious risk.
Never Share Your Seed Phrase
Your 12-24 word recovery phrase is the master key. No legitimate service will ever ask for it.
Scammers often impersonate support agents, create fake websites, or send phishing emails requesting your seed phrase. Remember: your seed phrase is equivalent to full access to your funds. Even hardware wallet manufacturers will never ask for it. If someone does, it is always a scam. Store it offline, never digitally, and never take a photo of it.
Use Official Firmware Only
Only update firmware through the manufacturer's official app. Never sideload firmware from other sources.
Malicious firmware can extract your private keys or redirect transactions to an attacker's address. Always download updates from the official Trezor Suite or Ledger Live applications. Verify firmware checksums when possible, and never install firmware shared via forums, emails, or third-party sites, even if they claim to offer new features.
Watch for Phishing Attacks
Always type wallet URLs manually. Never click links in emails or messages claiming to be from Trezor or Ledger.
Phishing attacks are the #1 way crypto users lose funds. Attackers create pixel-perfect replicas of wallet interfaces that steal your credentials or seed phrase on entry. Bookmark official sites and only use those bookmarks. Be especially wary after data breaches, as attackers use leaked email lists to send targeted phishing campaigns. Enable browser warnings for suspicious sites.
Important
Strongly recommended practices that significantly improve your security posture.
Verify Addresses On-Device
Always confirm transaction addresses on your hardware wallet screen, not just your computer.
Clipboard-hijacking malware can silently replace copied wallet addresses with an attacker's address. Your computer screen might show a compromised address while your hardware wallet displays the real destination. Always compare every character of the address on your device's trusted display before confirming any transaction.
Backup in Multiple Locations
Store seed phrase backups in 2-3 secure locations. Consider metal backup plates for fire/water resistance.
A single backup in one location is vulnerable to fire, flood, theft, or physical damage. Use metal seed storage plates (like Cryptosteel or Billfodl) that withstand extreme temperatures. Consider splitting your backup using Shamir's Secret Sharing if your wallet supports it. Store copies in separate geographic locations such as a home safe and a bank safety deposit box.
Practice Operational Security
Don't discuss your holdings publicly. Use a VPN when managing crypto. Keep your setup private.
Publicly sharing your portfolio size or wallet addresses makes you a target for social engineering, SIM-swap attacks, and even physical threats. Use a dedicated email for crypto accounts, enable 2FA with a hardware key (not SMS), and avoid accessing wallets on public Wi-Fi. The less information attackers have about you, the safer your funds are.
Use a Dedicated Device
Keep a separate computer or phone for crypto transactions. This reduces exposure to malware and phishing.
Your daily browsing device is exposed to countless attack vectors: malicious browser extensions, drive-by downloads, compromised websites, and infected email attachments. A dedicated device used only for crypto transactions dramatically shrinks your attack surface. Keep it updated, install minimal software, and never use it for general web browsing or email.
Recommended
Best practices that add extra layers of protection to your setup.
Test Recovery Regularly
Periodically verify you can restore from your backup. A backup you can't use is no backup at all.
At least once every 6 months, perform a dry-run recovery to ensure your seed phrase backup is correct and complete. You can do this by restoring on a spare device or using the wallet's recovery check feature without wiping your main device. This also helps you stay familiar with the recovery process so you can act quickly in an emergency.
Enable Passphrase Protection
Add a 25th word passphrase for an extra layer of security. This creates a hidden wallet even if your seed phrase is compromised.
A passphrase (sometimes called the 25th word) creates an entirely separate set of wallets tied to your seed phrase. Even if someone obtains your 24-word seed, they cannot access funds protected by a passphrase. Use a strong, memorable passphrase and store a backup of it separately from your seed phrase. Note: forgetting your passphrase means permanent loss of access to those funds.
Which Wallet Is Right for You?
What's your primary use case?
Buying guide
Check the features that matter most to you, and we'll recommend the best wallet
Your Best Match
Check items to see recommendations
Select the features that matter most to you from the checklist.
Community ratings
How real users rate each wallet across key categories
Trezor Safe 7
“Top-tier security in a premium package”
Trezor Safe 5
“Reliable workhorse for long-term holders”
Ledger Nano Gen5
“Best compact option for mobile users”
Ledger Flex
“Beautiful design meets solid security”
Ledger Stax
“Premium feel, but pricey for what you get”
Ratings compiled from community feedback across forums, app stores, and verified purchasers. Last updated March 2026.
How to choose
- 1Buy from official stores only.
- 2Set up offline, then verify backup words by hand.
- 3Use a passphrase if your threat model needs it.
- 4Test recovery before storing meaningful value.
FAQ
What are the latest Trezor and Ledger models in this list?
This page is now limited to Trezor and Ledger picks only, including Trezor Safe 7 and Trezor Safe 5, plus Ledger Nano Gen5, Ledger Flex, and Ledger Stax.
Is a hardware wallet the same as a cold wallet?
A hardware wallet is a type of cold wallet. Cold wallet means keys stay offline. Hardware wallets are the most practical cold-storage option for most users.
Can I recover funds if the device breaks?
Yes, if you still have your recovery phrase and optional passphrase. Your device can fail; your backup process is what protects the funds.
What matters most when choosing a hardware wallet?
Security model, backup workflow, and whether the signing flow matches how you actually use crypto. Fancy features matter less than reliable recovery.
Should beginners start with a hardware wallet?
If you hold meaningful value for the long term, yes. Start with a device known for clear onboarding and test recovery with a small amount first.
Secure storage first, tracking second
Once long-term holdings are moved to hardware storage, track performance without exposing private keys in hot-wallet workflows.
Editorial note: educational content only, not financial advice.